Security Tip: Don't Forget Your Registration Form!
[Tip#72] We talk a lot about protecting password reset and login forms, but don't forget about the humble registration form, it can provide attackers with crucial intel!

I was procrastinating browsing Twitter and came across this wonderful meme:
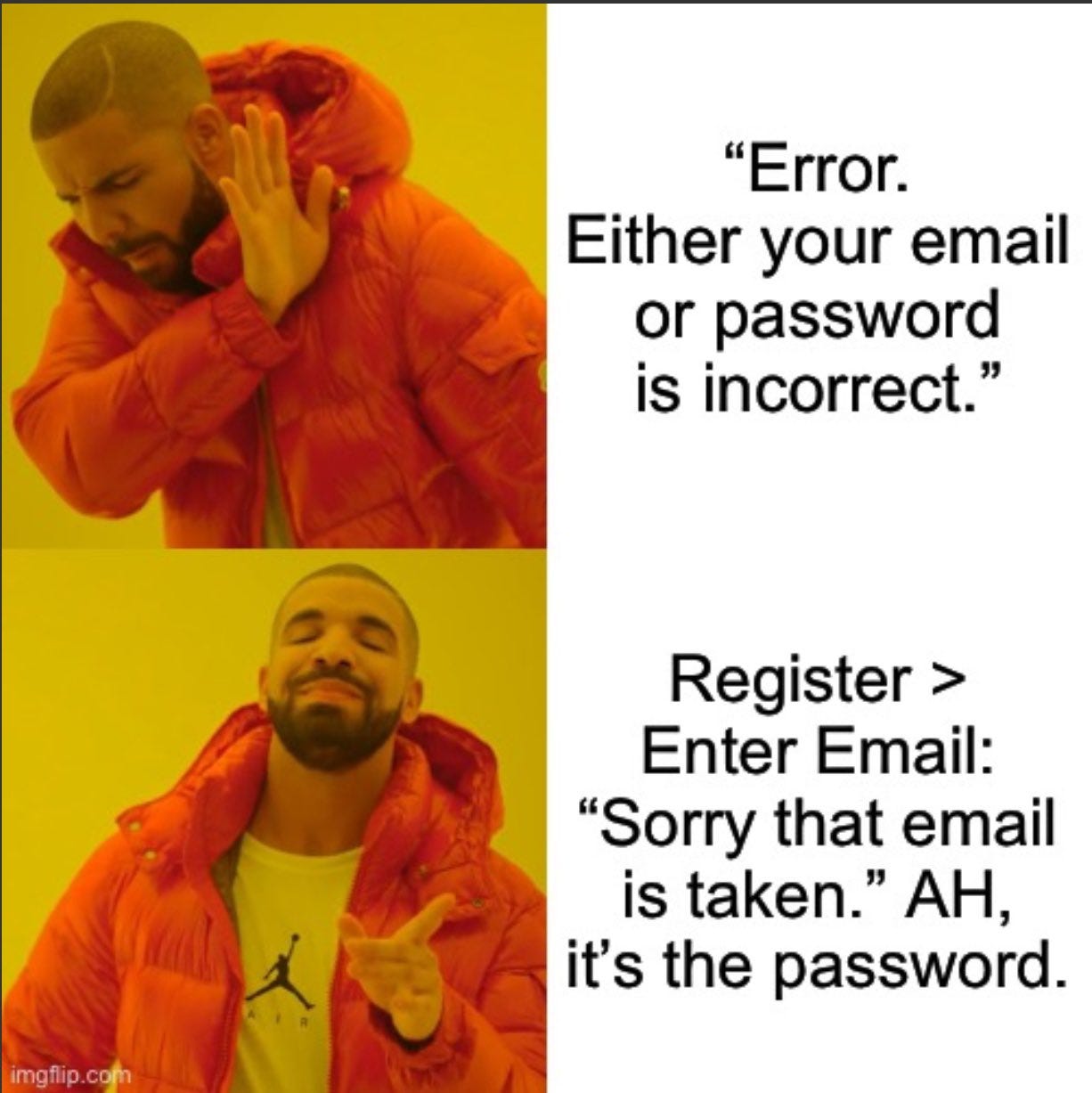
In the first panel we have what is presumably a login form error message, giving an ambiguous message to obfuscate which input is incorrect:
“Error. Either your email or password is incorrect.”
Followed by the response from the registration form, which confirms the email address is in the database:
Register > Enter Email: ”Sorry that email is taken.”
AH, it’s the password.
Upon seeing this, my first reaction was…
This is why ambiguous messaging on password reset forms is often pointless.
Folks spend so much time worrying about the password reset form leaking account existence and ensuring it has rate limiting, but what about the humble registration form?
Not only do they usually tell you if an email address is already in the database, but they also often lack sufficient rate limiting, and don’t send out any emails, so you can usually use a registration form to check if email addresses are in the database much faster and quieter than with a password reset form.
So this week, I want you to remember your humble registration form!
- Ensure it has rate limiting that includes any validation failures.
- If account attacks or credential stuffing are a concern, log those validation failures so you’re aware of malicious activity.
- If the existence of email addresses is supposed to be secret, don’t validate emails on the registration form!
However, if your app does need to protect user identities, your registration form shouldn’t validate email addresses. Instead, it should just collect all the user's information and notify the provided email address - either to inform the existing account owner of the attempt, or to confirm ownership of the address and continue the registration flow.
See In Depth: Registration Without Enumeration for more information on this topic.
If you found this security tip useful? 👍
Subscribe now to get weekly Security Tips straight to your inbox, filled with practical, actionable advice to help you build safer apps.
Want to learn more? 🤓
Upgrade to a Premium Subscription for exclusive monthly In Depth articles, or support my work with a one-off tip or recurring Sponsorship! Your support directly funds my security work in the Laravel community. 🥰
Need a second set of eyes on your code?
Book in a Laravel Security Audit and Penetration Test today! I also offer budget-friendly Security Reviews too.
Finally, connect with me on Bluesky, or other socials, and check out Practical Laravel Security, my interactive course designed to boost your Laravel security skills.





