OWASP Tip: A06:2021 – Vulnerable and Outdated Components
Keep your stuff updated!!
Greetings friends! Firstly, a big welcome to the new subscribers, it’s great to have you here! We’re currently in the middle of our OWASP Top 10 series, this week we’re covering risk #6, A06:2021 – Vulnerable and Outdated Components. If you’re new or have missed previous weeks, head over to the overview for links to each post.
🕵️ It’s important to audit the security of your apps, book in a Laravel Security Audit today!
Looking to learn more?
⏩ Security Tip #8: Sensitive Model Attributes
▶️ In Depth #3: Escaping Output Safely
A06:2021 – Vulnerable and Outdated Components
The title for this week’s OWASP Top 10 Risk, Vulnerable and Outdated Components, sounds pretty self-explanatory, and familiar - we’ve covered aspects of this topic many times before…
Ultimately, we want to keep our dependencies, frameworks, tooling, and infrastructure updated. Using old versions increases the likelihood of vulnerabilities being found and exploited to compromise your app. This is especially true if you’re using outdated and no-longer-supposed versions of things! Vulnerabilities are still discovered for unsupported versions of software all the time, but once security updates stop, all they get used for is to make hacking easier.
PHP Supported Versions
⚠️ PHP 7.4 stops receiving security updates on the 28th Nov 2022! ⚠️
That’s only 3 weeks from when this post will be published, so if you’re still running 7.4 (or earlier!!), make sure you update to 8.0 or 8.1 ASAP!
Check out https://www.php.net/supported-versions.php for the official list of PHP supported versions.
Laravel Supported Versions
⚠️ Laravel 8 stops receiving security updates on the 24th January 2023! ⚠️
That’s only 3 months away, so you’ve only got a bit of time left to organise your upgrades if you’re still on 8 (or earlier!!). But don’t leave it too late, upgrading Laravel can be a lot more involved than PHP or OS updates.
Check out Laravel’s Support Policy for more details.
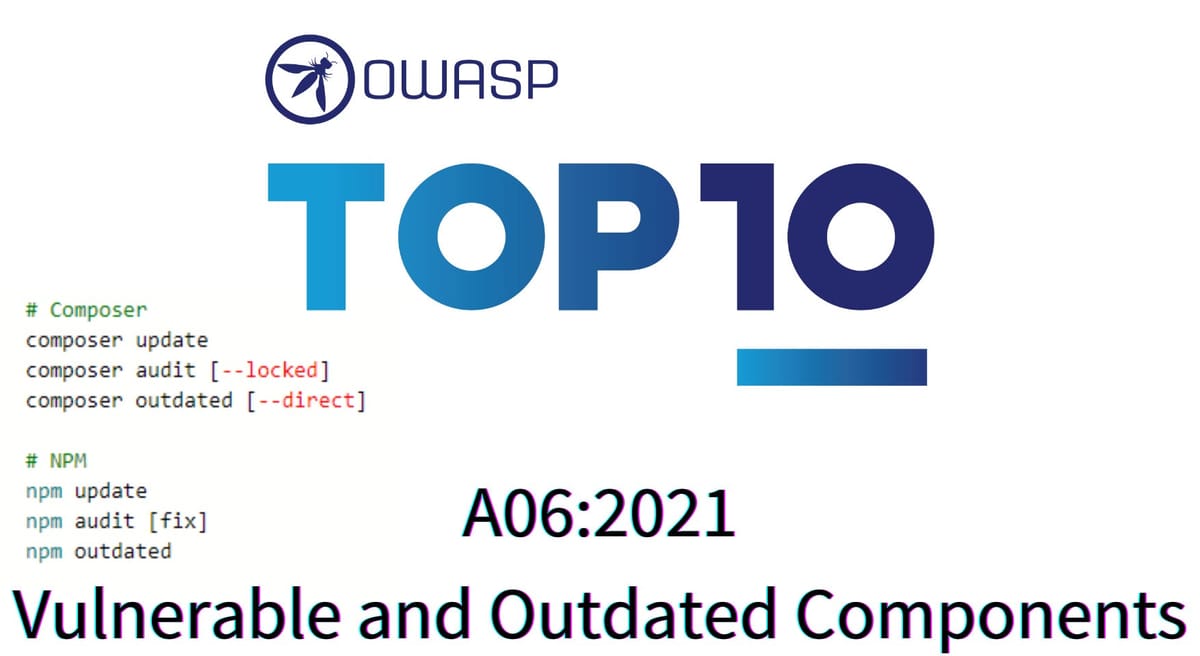
Composer
These are some of the commands you should be aware of to manage your dependencies.
composer updateUpdates dependencies to the latest available, as supported by your composer.json. Should be run regularly to ensure you’re getting the latest security updates.
For larger teams, it may make sense to designate one person on the team as the Composer Manager, and it’s their job to update composer weekly and ensure everything works. You could use a rotating schedule if you want to share the responsibility around.
composer audit [--locked]Checks your Composer dependencies for any known security vulnerabilities.1
Use the --locked flag to check versions in composer.lock, rather than what is installed.
composer outdated [--direct]Lists installed packages that have updates available, with indicators for the type of update (i.e. patch, minor, or major). Also indicates abandoned/depreciated packages, which should be considered unsafe.
The --direct flag reports only direct dependencies of your project, rather than all dependencies. This is helpful when you have a lot of dependencies and only want to see which ones you directly use are outdated.
NPM
These are some of the commands you should be aware of to manage your dependencies. You’ll notice they match Composer’s options. 😉
npm updateUpdates dependencies to the latest versions.
npm audit [fix]Checks your NPM dependencies for any known security vulnerabilities.
The optional fix directive allows NPM to automatically update vulnerable packages when it believes it’s safe to do so. You can add --force if you want it to upgrade everything, even with unsafe.
npm outdatedLists packages that have updates available, specifying the different versions available.
I covered this command in more detail here: https://securinglaravel.com/security-tip-composer-audit ↩